I posted last week about threats that are emerging hiding within he COVID-19 pandemic. There has been a surge of malware that will wipe your PC. Be careful regarding what you install. See my post about remote access best practices HERE.
ZDNET posted about some current campaigns that sol purpose is to destroy your computer. The original post can be found HERE.
With the coronavirus (COVID-19) pandemic raging all over the globe, some malware authors have developed malware that destroys infected systems, either by wiping files or rewriting a computer’s master boot record (MBR).
With help from the infosec community, ZDNet has identified at least five malware strains, some distributed in the wild, while others appear to have been created only as tests or jokes.
The common theme among all four samples is that they use a coronavirus-theme and they’re geared towards destruction, rather than financial gain.
MBR-rewriting malware
Of the four malware samples found by security researchers this past month, the most advanced were the two samples that rewrote MBR sectors.
Some advanced technical knowledge was needed to create these strains as tinkering with a master boot record is no easy feat and could easily result in systems that didn’t boot at all.
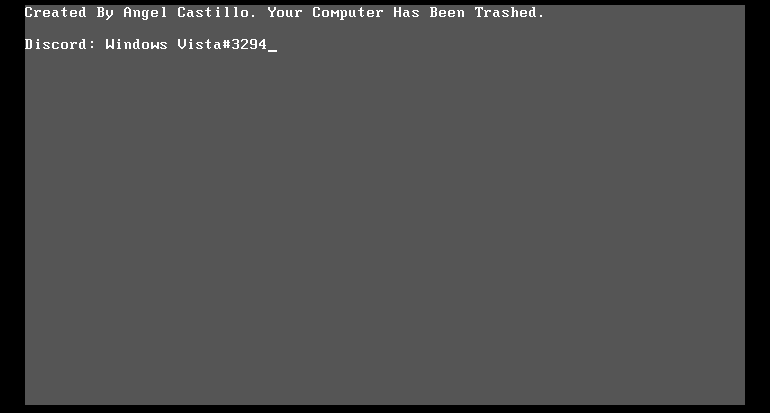
The first of the MBR-rewriters was discovered by a security researcher that goes by the name of MalwareHunterTeam, and detailed in a report from SonicWall this week. Using the name of COVID-19.exe, this malware infects a computer and has two infection stages.
In the first phase, it just shows an annoying window that users can’t close because the malware has also disabled the Windows Task Manager.
While users attempt to deal with this window, the malware is silently rewriting the computer’s master boot record behind their back. It then restarts the PC, and the new MBR kicks in, blocking users into a pre-boot screen.
Users can eventually regain access to their computers, but they’ll need special apps that can be used to recover and rebuild the MBR to a working state.
But there was a second coronavirus-themed malware strain that re-wrote the MBR. This one is a far more convoluted malware operation.
It posed as the “CoronaVirus ransomware” but it was only a facade. The malware’s primary function was to steal passwords from an infected host and then mimic ransomware to trick the user and mask its real purpose.
However, it wasn’t ransomware either. It only posed as one. Once the data-stealing operations ended, the malware entered into a phase where it rewrote the MBR, and blocked users into a pre-boot message, preventing access to their PCs. With users seeing ransom notes and then not being able to access their PCs, the last thing users would thing to do is to check if someone exfiltrated passwords from their apps.
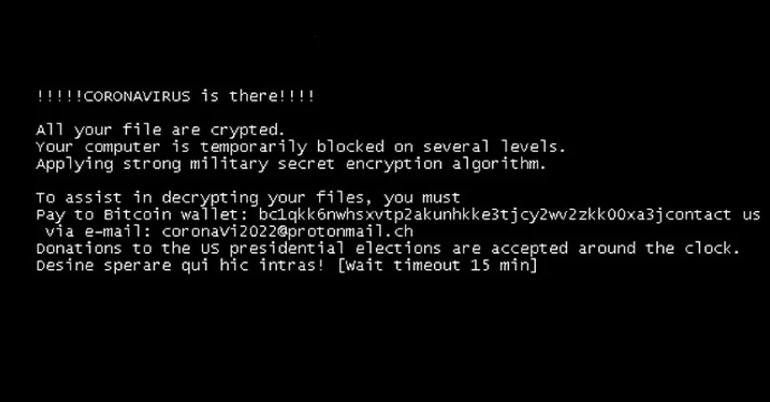
According to analysis from SentinelOne security researcher Vitali Kremez and Bleeping Computer, the malware also contained code to wipe files on the user’s systems, but this didn’t appear to be active in the version they analyzed.
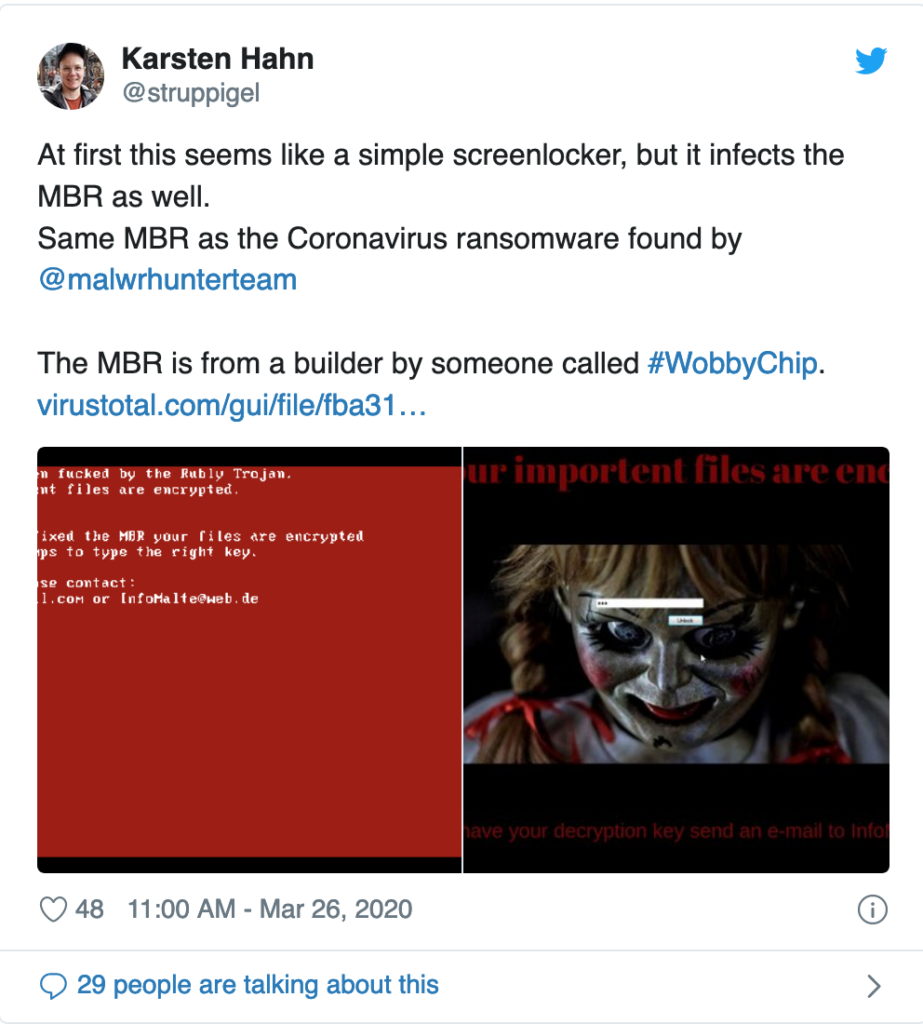
Furthermore, this one was also spotted twice, with a second version discovered by G DATA malware researcher Karsten Hahn, two weeks later. This time, the malware kept the MBR-rewriting capabilities but replaced the data wiping feature with a functional screen-locker.
Data wipers
But security researchers have spotted more than coronavirus-themed MBR-rewriters. They also spotted two data wipers.
Both were discovered by MalwareHunterTeam.
The first was spotted back in February. It used a Chinese file name, and most likely targeted Chinese users, although we don’t have information if it was distributed in the wild or was just a test.
The second was spotted yesterday, and this one was found uploaded on the VirusTotal portal by someone located in Italy.
MalwareHunterTeam described both strains as “poor wipers” because of the inefficient, error-prone, and time-consuming methods they used to erase files on infected systems. However, they worked, which made them dangerous if ever spread in the wild.

It might seem weird that some malware authors create destructive malware like this, but it’s not the first time that this happened. For every financially-motivated malware strain that security researchers discover, there’s also one that was created as a joke, just for the giggles. Something similar happened during the WannaCry ransomware outbreak in 2017, when days after the original WannaCry ransomware encrypted computers all over the world, there were countless of clones doing the same thing for no apparent reason.



