Cisco Systems just released the 2015 Midyear Security Report found HERE. This report provides an overview of major threats observed in the first half of 2015. There are also parts that look at future trends and offers for small, midsize and enterprise organizations. Topics on the latest threats include exploit kits, Microsoft office exploits, malware research, java exploits and so on. Its free to download. Check it out.
Here are some highlights from the report.
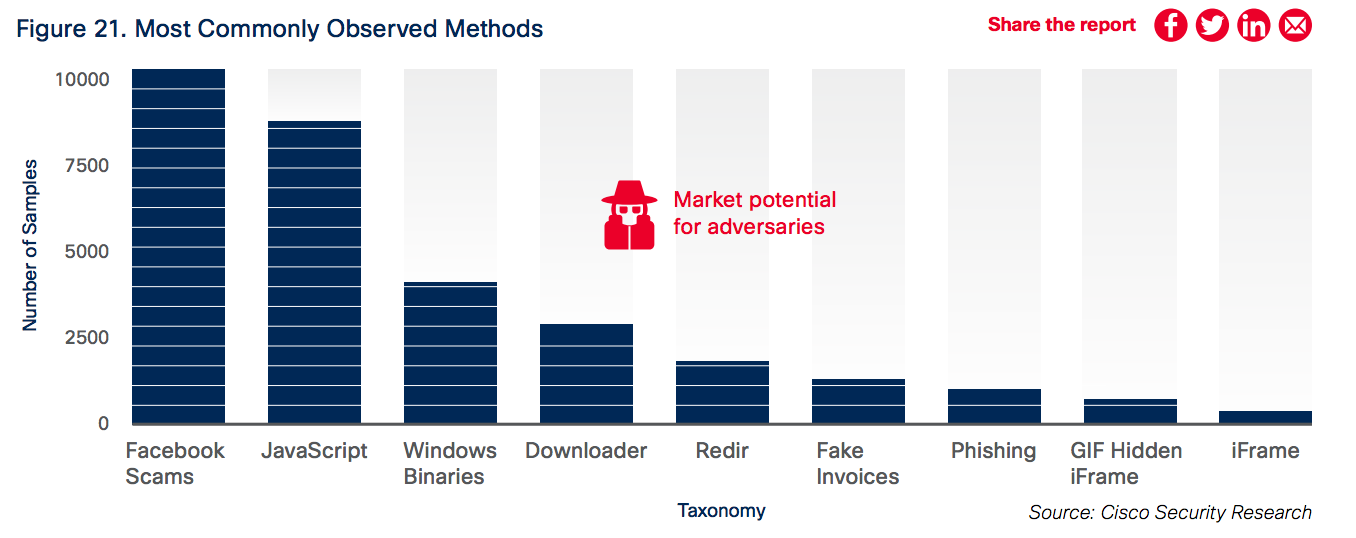
I like this chart showing the most commonly observed attack methods.
● Exploits of Adobe Flash vulnerabilities are increasing. They are regularly integrated into widely used exploit kits such as Angler and Nuclear.
● Angler continues to lead the exploit kit market in terms of overall sophistication and effectiveness.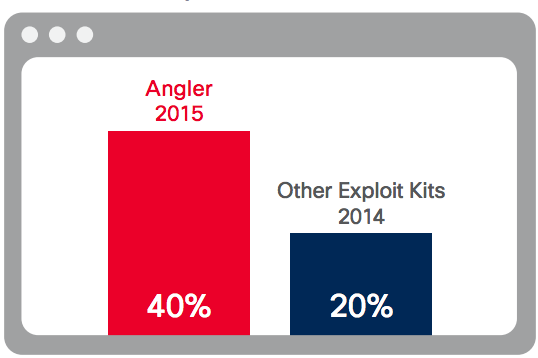
● Operators of crimeware, like ransomware, are hiring and funding professional development teams to help them make sure their tactics remain profitable.
● Criminals are turning to the anonymous web network Tor and the Invisible Internet Project (I2P) to relay command-and-control communications while evading detection.
● Adversaries are once again using Microsoft Office macros to deliver malware. It’s an old tactic that fell out of favor, but it’s being taken up again as malicious actors seek new ways to thwart security protections.
● Some exploit kit authors are incorporating text from Jane Austen’s classic novel Sense and Sensibility into web landing pages that host their exploit kits. Antivirus and other security solutions are more likely to categorize these pages as legitimate after “reading” such text.
● Malware authors are increasing their use of techniques such as sandbox detection to conceal their presence on networks.
● Spam volume is increasing in the United States, China, and the Russian Federation, but remained relatively stable in other regions in the first five months of 2015.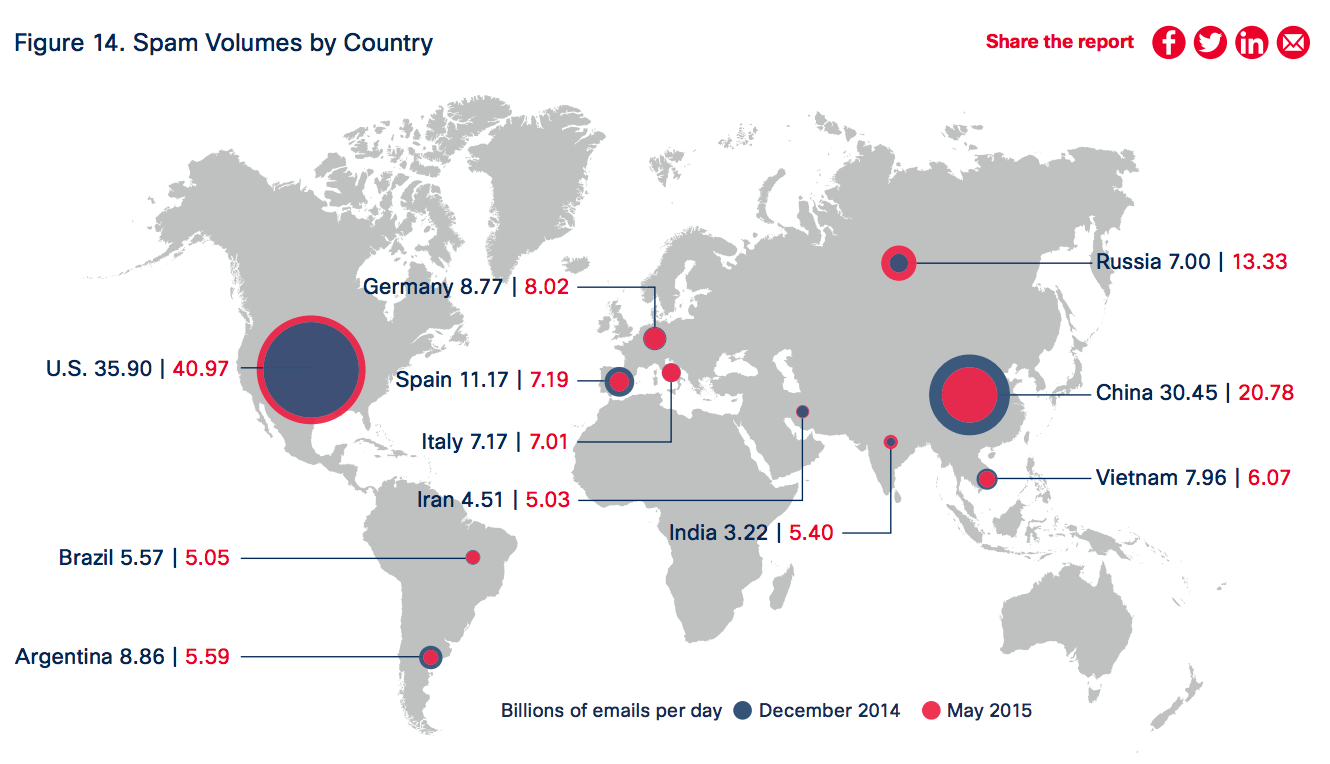
● The security industry is paying more attention to mitigating vulnerabilities in open-source solutions.
● Continuing a trend covered in the Cisco 2015 Annual Security Report, exploits involving Java have been on the decline in the first half of 2015.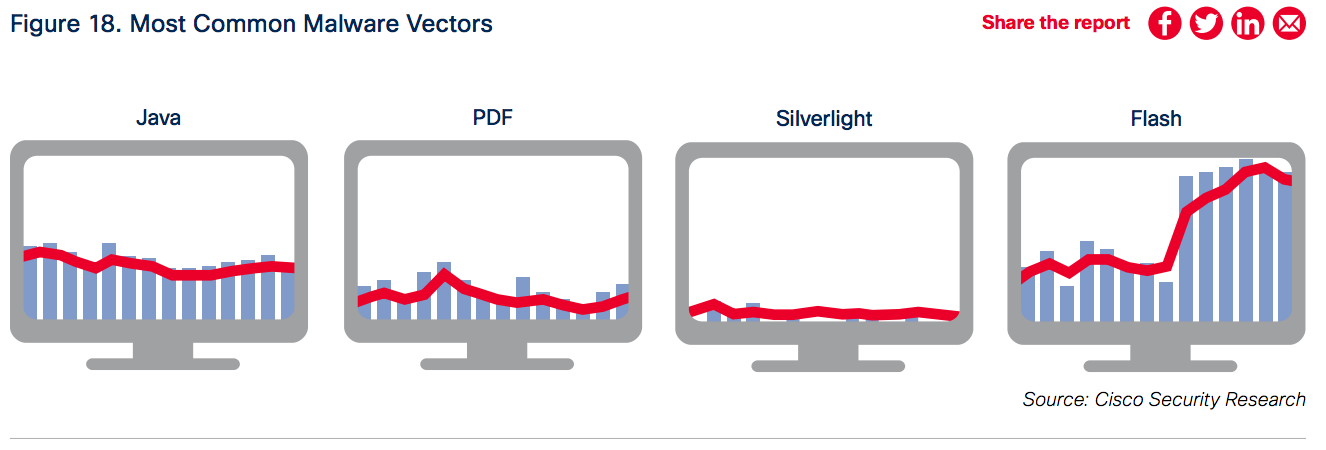




Which one do you think is the best model of cisco asa?
All models offer the same features. The sizing depends on throughput and things like hardware HA features such as redundant power supplies. All models from the 5506 to large 5585s can be firewalls, application firewalls, content filters, IPS and day zero network tools.